Mdm Iphone Do Not Allow Images to Be Uploaded
This browser is no longer supported.
Upgrade to Microsoft Border to have advantage of the latest features, security updates, and technical support.
iOS and iPadOS device settings to utilise common iOS/iPadOS features in Intune
Intune includes some built-in settings to permit iOS/iPadOS users to use different Apple features on their devices. For instance, you can command AirPrint printers, add apps and folders to the dock and home screen pages, show app notifications, bear witness asset tag details on the lock screen, use single sign-on authentication, and use certificate authentication.
Use these features to control iOS/iPadOS devices as role of your mobile device management (MDM) solution.
This commodity lists these settings, and describes what each setting does. For more information on these features, become to Add iOS/iPadOS or macOS device characteristic settings.
Before you lot begin
Create an iOS/iPadOS device features configuration contour.
Note
These settings apply to unlike enrollment types, with some settings applying to all enrollment options. For more information on the different enrollment types, run into iOS/iPadOS enrollment.
AirPrint
Settings apply to: All enrollment types
Annotation
Exist sure to add all printers to the same contour. Apple prevents multiple AirPrint profiles from targeting the same device.
- IP address: Enter the IPv4 or IPv6 accost of the printer. If you use hostnames to place printers, y'all can become the IP address by pinging the printer in the last. Get the IP address and path (in this article) provides more than details.
- Resource path: The path is typically
ipp/printfor printers on your network. Become the IP address and path (in this article) provides more details. - Port: Enter the listening port of the AirPrint destination. If you leave this property blank, AirPrint uses the default port. Available on iOS eleven.0+, and iPadOS 13.0+.
- Strength TLS: Enable secures AirPrint connections with Transport Layer Security (TLS). Available on iOS 11.0+, and iPadOS thirteen.0+.
To add AirPrint servers, you can:
- Enter printer details to add an AirPrint destination to the listing. Many AirPrint servers tin can be added.
- Import a comma-separated file (.csv) with this data. Or, Export to create a list of the AirPrint servers you added.
Get server IP address, resource path, and port
To add together AirPrinter servers, you need the IP address of the printer, the resource path, and the port. The following steps show you how to get this information.
-
On a Mac that's connected to the same local network (subnet) as the AirPrint printers, open up Terminal (from /Applications/Utilities).
-
In the Terminal, type
ippfind, and select enter.Note the printer information. For example, it may return something similar to
ipp://myprinter.local.:631/ipp/port1. The first role is the name of the printer. The last function (ipp/port1) is the resource path. -
In the Concluding, type
ping myprinter.local, and select enter.Note the IP address. For instance, it may return something similar to
PING myprinter.local (10.50.25.21). -
Employ the IP address and resource path values. In this example, the IP address is
10.50.25.21, and the resource path is/ipp/port1.
Dwelling house screen layout
This characteristic applies to:
- iOS nine.iii or newer
- iPadOS xiii.0 and newer
- Automated device enrollment (supervised)
Note
-
Merely add an app once to the dock, page, folder on a page, or folder in the dock. Adding the same app in any 2 places prevents the app from showing on devices, and may show reporting errors.
For example, if you add together the camera app to a dock and a page, the camera app isn't shown, and reporting might show an error for the policy. To add the camera app to the home screen layout, choose only the dock or a page, not both.
-
When you lot apply a home screen layout, it overwrites any user-defined layout. And so, information technology'south recommended to utilise home screen layouts on userless devices.
-
You can accept preexisting apps installed on the device that are non included in the home screen layout configuration. These apps are shown in alphabetical order after the configured apps.
Habitation screen
Utilise this feature to add together apps. And, run across how these apps look on pages, the dock, and within folders. It likewise shows you the app icons. Volume Purchase Program (VPP) apps, line-of business apps, and web link apps (spider web app URLs) are populated from the client apps you add.
-
Layout size: Choose an appropriate filigree size for the device'southward abode screen. An app or folder takes up one identify in the grid. If the target device doesn't support the selected size, some apps may not fit and will be pushed to the next available position on a new page. For reference:
-
iPhone 6 and afterward support 4 columns ten six rows
-
iPhone 5 supports 4 columns x v rows
-
iPads support 5 columns x 6 rows
-
-
+: Select the add together button to add apps.
-
Create binder or add apps: Add an App or a Binder:
-
App: Select existing apps from the list. This selection adds apps to the home screen on devices. If you don't accept any apps, then Add apps to Intune.
You lot can also search for apps past the app name, such every bit
authenticatorordrive. Or, search past the app publisher, such asMicrosoftorApple tree. -
Binder: Adds a binder to the dwelling screen. Enter the Binder proper noun, and select existing apps from the listing to go in the folder. This folder proper name is shown to users on their devices.
You can too search for apps by the app name, such as
authenticatorordrive. Or, search by the app publisher, such asMicrosoftorApple.Apps are bundled from left to correct, and in the aforementioned order as shown. Apps can be moved to other positions. You tin but have one folio in a binder. As a work around, add ix (9) or more than apps to the folder. Apps are automatically moved to the next folio. Yous can add together any combination of VPP apps, web links (spider web apps), store apps, line-of-business apps, and organisation apps.
-
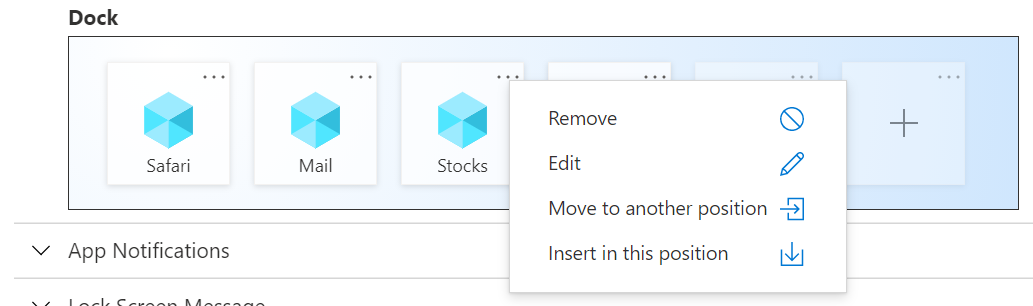
Dock
Add upward to 4 (4) items for iPhones, and up to six (half dozen) items for iPads (apps and folders combined) to the dock on the screen. Many devices support fewer items. For example, iPhone devices support up to four items. So, only the outset four items you add together are shown.
-
+: Select the add together button to add apps or folders to the dock.
-
Create folder or add apps: Add an App or a Binder:
-
App: Select existing apps from the list. This option adds apps to the dock on the screen. If yous don't take whatsoever apps, so Add apps to Intune.
Y'all can also search for apps by the app name, such as
authenticatorordrive. Or, search by the app publisher, such asMicrosoftorApple. -
Binder: Adds a folder to the dock on the screen. Enter the Folder proper name, and select existing apps from the listing to get in the binder. This folder name is shown to users on their devices.
You lot can also search for apps by the app proper noun, such equally
authenticatororbulldoze. Or, search by the app publisher, such every bitMicrosoftorApple.Apps are arranged from left to right, and in the same order as shown. Apps can exist moved to other positions. If you add more apps than can fit on a folio, and then the apps are automatically moved to another page. You tin can add up to 20 pages in a folder on the dock. You can add together any combination of VPP apps, web links (web apps), shop apps, line-of-concern apps, and system apps.
-
Notation
When you apply the Home Screen Layout settings to add together pages, or add together pages and apps to the dock, the icons on the Domicile Screen and pages are locked. They tin can't be moved or deleted. This behavior might exist by design with iOS/iPadOS and Apple tree'due south MDM policies.
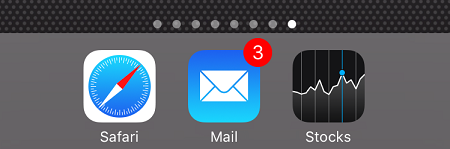
Example
In the post-obit case, the dock screen shows the Safari, Postal service, and Stocks apps. The Stocks app is selected to show its properties:
When you assign the policy to an iPhone, the dock looks similar to the post-obit epitome:
App notifications
Settings use to: Automated device enrollment (supervised)
-
Add: Add notifications for apps:
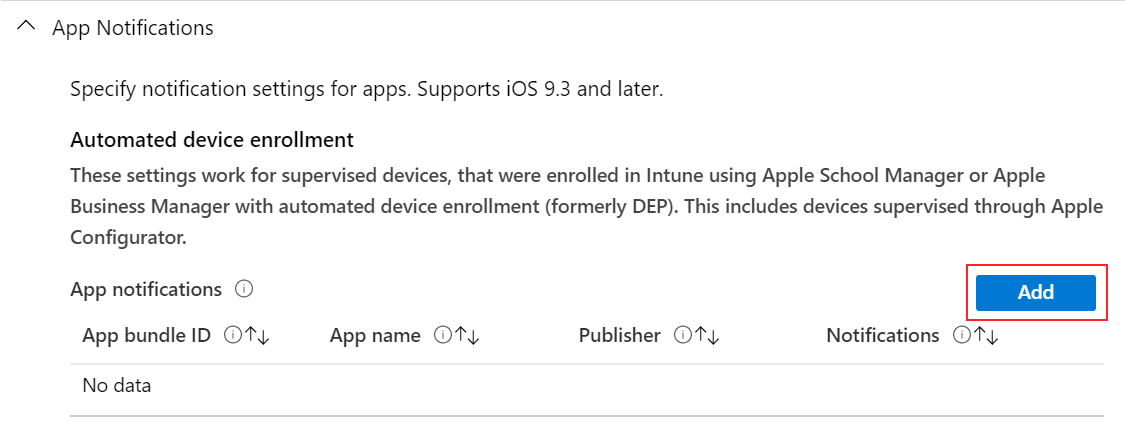
- App bundle ID: Enter the App Package ID of the app you desire to add. See Parcel IDs for built-in iOS/iPadOS apps for some examples.
- App proper noun: Enter the name of the app y'all desire to add. This name is used for your reference in the Microsoft Endpoint Managing director admin eye. Information technology isn't shown on devices.
- Publisher: Enter the publisher of the app you're calculation. This name is used for your reference in the Microsoft Endpoint Managing director admin center. It isn't shown on devices.
- Notifications: Enable or Disable the app from sending notifications to devices.
-
Bear witness in notifications middle: Enable allows the app to show notifications in the device Notification Center. Disable prevents the app from showing notifications in the Notification Heart.
-
Show on Lock Screen: Enable shows app notifications on the device lock screen. Disable prevents the app from showing notifications on the lock screen.
-
Alarm type: When devices are unlocked, choose how the notification is shown. Your options:
- None: No notification is shown.
- Banner: A imprint is briefly shown with the notification.
- Modal: The notification is shown and users must manually dismiss information technology before continuing to use the device.
-
Badge on app icon: Select Enable to add a badge to the app icon. The bluecoat means the app sent a notification.
-
Enable sounds: Select Enable to play a sound when a notification is delivered.
-
Evidence previews: Shows a preview of contempo app notifications. Select when to show the preview. The value y'all cull overrides the user configured value on the device (Settings > Notifications > Show Previews). Your options:
- Non configured: Intune doesn't change or update this setting.
- When unlocked: The preview only shows when the device is unlocked.
- Ever: The preview always shows on the lock screen.
- Never: The preview never shows.
This feature applies to:
- iOS/iPadOS xiv.0 and newer
-
Lock screen message
This feature applies to:
- iOS ix.3 and later
- iPadOS 13.0 and newer
Settings apply to: Automated device enrollment (supervised)
-
"If Lost, Return to..." Message: If devices are lost or stolen, enter a note that might help get the device returned if found. You can enter any text y'all want. For case, enter something similar
If found, phone call Contoso at ....The text you enter is shown on the sign in window and lock screen on devices.
-
Asset tag information: Enter information about the asset tag of the device. For example, enter
Owned by Contoso CorporSerial Number: {{serialnumber}}.Device tokens can also be used to add device-specific information to these fields. For example, to testify the series number, enter
Serial Number: {{serialnumber}}orDevice ID: {{DEVICEID}}. On the lock screen, the text shows similar toSerial Number 123456789ABC. When entering variables, be certain to apply curly brackets{{ }}.The following device information variables are supported:
-
{{AADDeviceId}}: Azure Ad device ID -
{{AccountId}}: Intune tenant ID or account ID -
{{AccountName}}: Intune tenant name or account name -
{{AppleId}}: Apple tree ID of the user -
{{Section}}: Section assigned during Setup Banana -
{{DeviceId}}: Intune device ID -
{{DeviceName}}: Intune device name -
{{domain}}: Domain proper name -
{{EASID}}: Commutation Active Sync ID -
{{EDUUserType}}: Type of user -
{{IMEI}}: IMEI of the device -
{{mail}}: Email address of the user -
{{ManagedAppleId}}: Managed Apple ID of the user -
{{MEID}}: MEID of the device -
{{partialUPN}}: UPN prefix before the @ symbol -
{{SearchableDeviceKey}}: NGC Key ID -
{{SerialNumber}}: Device serial number -
{{SerialNumberLast4Digits}}: Last four digits of the device serial number -
{{SIGNEDDEVICEID}}: Device ID blob assigned to client during Company Portal enrollment -
{{SignedDeviceIdWithUserId}}: Device ID hulk assigned to customer with user-affinity during Apple Setup Assistant -
{{UDID}}: Device UDID -
{{UDIDLast4Digits}}: Last iv digits of the device UDID -
{{UserId}}: Intune user ID -
{{UserName}}: User name -
{{userPrincipalName}}: UPN of the user
Note
Variables aren't validated in the UI, and are instance sensitive. Every bit a result, you may see profiles saved with incorrect input. For instance, if you enter
{{DeviceID}}instead of{{deviceid}}or '{{DEVICEID}}', so the literal cord is shown instead of the device's unique ID. Be sure to enter the correct information. All lowercase or all uppercase variables are supported, but not a mix. -
Single sign-on
Settings apply to: Device enrollment, Automatic device enrollment (supervised)
-
Realm: Enter the domain role of the URL. For example, enter
contoso.com. -
Azure Advert username attribute: Intune looks for this aspect for each user in Azure AD. Intune and then populates the corresponding field (such as UPN) before generating the XML that gets installed on devices. Your options:
-
Not configured: Intune doesn't change or update this setting. By default, the OS will prompt users for a Kerberos principal name when the profile is deployed to devices. A principal name is required for MDMs to install SSO profiles.
-
User principal name: The user principal proper noun (UPN) is parsed in the following style:
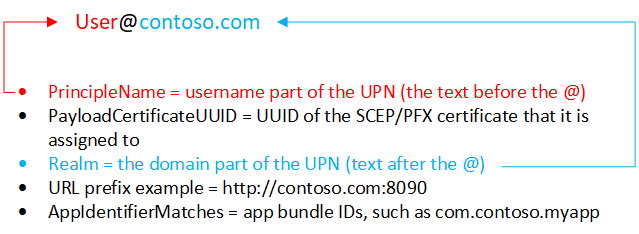
Yous can also overwrite the realm with the text you enter in the Realm text box.
For case, Contoso has several regions, including Europe, Asia, and North America. Contoso wants their Asia users to apply SSO, and the app requires the UPN in the
username@asia.contoso.comformat. When y'all select User Principal Name, the realm for each user is taken from Azure AD, which iscontoso.com. So for users in Asia, select User Principal Proper noun, and enterasia.contoso.com. The user'due south UPN becomesusername@asia.contoso.com, instead ofusername@contoso.com. -
Intune device ID: Intune automatically selects the Intune Device ID.
Past default, apps only need to use the device ID. Simply if your app uses the realm and the device ID, you can type the realm in the Realm text box.
Note
By default, continue the realm empty if you employ device ID.
-
Azure Advertisement device ID
-
SAM business relationship proper name: Intune populates the on-premises Security Accounts Manager (SAM) business relationship proper name.
-
-
Apps: Add together apps on users devices that can utilize single sign-on.
The
AppIdentifierMatchesarray must include strings that friction match app bundle IDs. These strings may be exact matches, such equallycom.contoso.myapp, or enter a prefix match on the parcel ID using the * wildcard grapheme. The wildcard graphic symbol must appear later on a period graphic symbol (.), and may appear only once, at the end of the string, such ascom.contoso.*. When a wildcard is included, whatsoever app whose parcel ID begins with the prefix is granted admission to the business relationship.Use App Proper noun to enter a user-friendly name to help y'all identify the bundle ID.
-
URL prefixes: Add any URLs in your organization that require user single sign-on authentication.
For example, when a user connects to any of these sites, the iOS/iPadOS device uses the single sign-on credentials. Users don't need to enter any additional credentials. If multi-factor authentication is enabled, then users are required to enter the 2nd hallmark.
Note
These URLs must exist properly formatted FQDN. Apple requires these to be in the
http://<yourURL.domain>format.The URL matching patterns must begin with either
http://orhttps://. A simple string match is run, and so thehttp://world wide web.contoso.com/URL prefix doesn't luciferhttp://www.contoso.com:fourscore/. With iOS 10.0+ and iPadOS 13.0+, a single wildcard * may be used to enter all matching values. For example,http://*.contoso.com/matches bothhttp://shop.contoso.com/andhttp://www.contoso.com.The
http://.comandhttps://.compatterns match all HTTP and HTTPS URLs, respectively. -
Credential renewal document: If using certificates for authentication (non passwords), select the existing SCEP or PFX certificate as the hallmark certificate. Typically, this certificate is the aforementioned certificate that'southward deployed to users for other profiles, such as VPN, Wi-Fi, or electronic mail.
Spider web content filter
Settings apply to: Automated device enrollment (supervised)
-
Filter Blazon: Choose to let specific spider web sites. Your options:
-
Configure URLs: Utilize Apple tree's born web filter that looks for adult terms, including profanity and sexually explicit language. This feature evaluates each web page equally it's loaded, and identifies and blocks unsuitable content. You lot can also add URLs that you don't want checked past the filter. Or, block specific URLs, regardless of Apple tree's filter settings.
-
Permitted URLs: Add the URLs you want to allow. These URLs featherbed Apple's web filter.
Notation
The URLs y'all enter are the URLs you don't want evauluated by the Apple web filter. These URLs aren't a list of allowed web sites. To create a listing of allowed websites, set the Filter Blazon to Specific websites just.
-
Blocked URLs: Add the URLs you want to end from opening, regardless of the Apple spider web filter settings.
-
-
Specific websites only (for the Safari web browser just): These URLs are added to the Safari browser'south bookmarks. Users are only allowed to visit these sites; no other sites can be opened. Utilise this pick but if y'all know the verbal listing of URLs that users tin access.
- URL: Enter the URL of the website y'all want to allow. For example, enter
https://www.contoso.com. - Bookmark Path: Apple changed this setting. All bookmarks get into the Allowed Sites folder. Bookmarks don't go in to the bookmark path you enter.
- Title: Enter a descriptive championship for the bookmark.
If yous don't enter any URLs, and then users can't admission any websites except for
microsoft.com,microsoft.cyberspace, andapple.com. These URLs are automatically allowed past Intune. - URL: Enter the URL of the website y'all want to allow. For example, enter
-
Single sign-on app extension
This feature applies to:
- iOS 13.0 and later
- iPadOS thirteen.0 and later
Settings utilize to: All enrollment types
-
SSO app extension type: Choose the type of SSO app extension. Your options:
-
Not configured: Intune doesn't alter or update this setting. By default, the OS doesn't use app extensions. To disable an app extension, you can switch the SSO app extension blazon to Non configured.
-
Microsoft Azure AD: Uses the Microsoft Enterprise SSO plug-in, which is a redirect-type SSO app extension. This plug-in provides SSO for Active Directory accounts across all applications that support Apple'south Enterprise Unmarried Sign-On feature. Use this SSO app extension type to enable SSO on Microsoft apps, organisation apps, and websites that authenticate using Azure Ad.
Of import
The Microsoft Azure Advertizing SSO extension is in public preview. This preview version is provided without a service level agreement (SLA). Information technology's not recommended to use in production. Certain features might not be supported, or might take restricted behavior. For more information, meet Supplemental Terms of Use for Microsoft Azure Previews.
The SSO plug-in acts as an advanced authentication banker that offers security and user experience improvements. All apps that use the Microsoft Authenticator app for authentication continue to get SSO with the Microsoft Enterprise SSO plug-in for Apple devices.
Of import
To achieve SSO with the Microsoft Azure Advert SSO app extension type, get-go install the iOS/iPadOS Microsoft Authenticator app on devices. The Authenticator app delivers the Microsoft Enterprise SSO plug-in to devices, and the MDM SSO app extension settings activate the plug-in. Once Authenticator and the SSO app extension profile are installed on devices, users must enter their credentials to sign in, and institute a session on their devices. This session is and then used across unlike applications without requiring users to authenticate once more. For more information about Authenticator, run into What is the Microsoft Authenticator app.
-
Redirect: Employ a generic, customizable redirect app extension to employ SSO with modernistic authentication flows. Be sure yous know the extension ID for your organization'south app extension.
-
Credential: Use a generic, customizable credential app extension to employ SSO with challenge-and-response hallmark flows. Be sure you know the extension ID for your organization'southward app extension.
-
Kerberos: Use Apple's built-in Kerberos extension, which is included on iOS 13.0+ and iPadOS 13.0+. This option is a Kerberos-specific version of the Credential app extension.
Tip
With the Redirect and Credential types, you add your own configuration values to laissez passer through the extension. If y'all're using Credential, consider using built-in configuration settings provided by Apple tree in the Kerberos blazon.
After users successfully sign in to the Authenticator app, they aren't prompted to sign in to other apps that employ the SSO extension. The first time users open managed apps that don't use the SSO extension, they're prompted to select the account that'southward signed in.
-
-
Enable shared device mode (Microsoft Azure AD only): Choose Aye if you're deploying the Microsoft Enterprise SSO plug-in to iOS/iPadOS devices configured for Azure Advertizement'south shared device mode feature. Devices in shared mode permit many users to globally sign in and out of applications that support shared device mode. When set to Not configured, Intune doesn't modify or update this setting. Past default, iOS/iPadOS devices aren't intended to be shared amid multiple users.
For more information about shared device mode and how to enable it, see Overview of shared device style and Shared device mode for iOS devices.
This feature applies to:
- iOS/iPadOS xiii.5 and newer
-
Extension ID (Redirect and Credential): Enter the package identifier that identifies your SSO app extension, such as
com.apple.extensiblesso. -
Squad ID (Redirect and Credential): Enter the team identifier of your SSO app extension. A team identifier is a 10-graphic symbol alphanumerical (numbers and letters) string generated by Apple, such every bit
ABCDE12345. The team ID isn't required.Locate your Team ID (opens Apple's website) has more than information.
-
Realm (Credential and Kerberos): Enter the name of your authentication realm. The realm name should exist capitalized, such every bit
CONTOSO.COM. Typically, your realm name is the same as your DNS domain name, simply in all upper-case letter. -
Domains (Credential and Kerberos): Enter the domain or host names of the sites that can cosign through SSO. For example, if your website is
mysite.contoso.com, thenmysiteis the host name, and.contoso.comis the domain name. When users connect to whatever of these sites, the app extension handles the authentication challenge. This hallmark allows users to use Face ID, Touch ID, or Apple tree pincode/passcode to sign in.- All the domains in your single sign-on app extension Intune profiles must be unique. You tin can't repeat a domain in any sign-on app extension profile, even if you're using different types of SSO app extensions.
- These domains aren't instance-sensitive.
- The domain must begin with a period (
.).
-
URLs (Redirect only): Enter the URL prefixes of your identity providers on whose behalf the redirect app extension uses SSO. When users are redirected to these URLs, the SSO app extension intervenes and prompts SSO.
- All the URLs in your Intune single sign-on app extension profiles must be unique. You tin't echo a domain in any SSO app extension contour, fifty-fifty if yous're using different types of SSO app extensions.
- The URLs must begin with
http://orhttps://.
-
Additional configuration (Microsoft Azure Ad, Redirect, and Credential): Enter additional extension-specific information to laissez passer to the SSO app extension:
-
Key: Enter the name of the item y'all desire to add, such as
user nameor 'AppAllowList'. -
Type: Enter the type of data. Your options:
- String
- Boolean: In Configuration value, enter
TruthfulorFaux. - Integer: In Configuration value, enter a number.
-
Value: Enter the data.
-
Add: Select to add your configuration keys.
-
-
Block keychain usage (Kerberos only): Yes prevents passwords from beingness saved and stored in the keychain. If blocked, users aren't prompted to relieve their countersign, and need to reenter the password when the Kerberos ticket expires. When set to Not configured (default), Intune doesn't alter or update this setting. Past default, the OS might allow passwords to be saved and stored in the keychain. Users aren't prompted to reenter their countersign when the ticket expires.
-
Crave Face ID, Touch ID, or passcode (Kerberos but): Yes forces users to enter their Face ID, Affect ID, or device passcode when the credential is needed to refresh the Kerberos ticket. When prepare to Not configured (default), Intune doesn't change or update this setting. Past default, the Os might not require users to use biometrics or device passcode to refresh the Kerberos ticket. If Keychain usage is blocked, then this setting doesn't employ.
-
Set as default realm (Kerberos merely): Yes sets the Realm value you entered every bit the default realm. When fix to Not configured (default), Intune doesn't change or update this setting. By default, the Os might not set a default realm.
Tip
- Select Yep for this setting if you're configuring multiple Kerberos SSO app extensions in your organisation.
- Select Yes for this setting if yous're using multiple realms. It sets the Realm value you lot entered as the default realm.
- If yous but accept one realm, leave information technology Not configured (default).
-
Block Autodiscover (Kerberos just): Yeah prevents the Kerberos extension from automatically using LDAP and DNS to decide its Active Directory site name.
-
Let just managed apps (Kerberos simply): When set to Yes, the Kerberos extension allows just managed apps, and any apps entered with the app packet ID to access the credential. When gear up to Not configured (default), Intune doesn't change or update this setting. Past default, the OS might let not-managed apps to access the credential.
This feature applies to:
- iOS/iPadOS xiv and newer
-
Principal proper name (Kerberos only): Enter the username of the Kerberos principal. Y'all don't need to include the realm name. For example, in
user@contoso.com,useris the principal proper noun, andcontoso.comis the realm proper name.Tip
- Yous tin also apply variables in the primary name by inbound curly brackets
{{ }}. For example, to show the username, enterUsername: {{username}}. - Nonetheless, be careful with variable commutation because variables aren't validated in the UI and they are case sensitive. Be sure to enter the correct data.
- Yous tin also apply variables in the primary name by inbound curly brackets
-
Agile Directory site code (Kerberos only): Enter the proper noun of the Agile Directory site that the Kerberos extension should use. You may not need to change this value, as the Kerberos extension may automatically detect the Active Directory site code.
-
Cache name (Kerberos simply): Enter the Generic Security Services (GSS) name of the Kerberos cache. You nigh likely don't need to set this value.
-
Sign in window text (Kerberos only): Enter the text shown to users at the Kerberos sign in window.
This feature applies to:
- iOS/iPadOS 14 and newer
-
App bundle IDs (Microsoft Azure AD, Kerberos): Enter the bundle IDs of the additional apps that should get single sign-on through an extension on your devices.
If you use the Microsoft Azure Advert SSO app extension type, then:
-
These apps use the Microsoft Enterprise SSO plug-in to authenticate the user without requiring a sign-in.
-
The app bundle IDs you enter accept permission to use the Microsoft Azure Advertizement SSO app extension if they don't use any Microsoft libraries, such every bit Microsoft Authentication Library (MSAL).
The feel for these apps may not exist as seamless compared to the Microsoft libraries. Older apps that employ MSAL hallmark, or apps that don't utilize the newest Microsoft libraries, must be added to this listing to piece of work properly with the Microsoft Azure SSO app extension.
If you use the Kerberos SSO app extension blazon, and then these apps:
- Have access to the Kerberos Ticket Granting Ticket
- Have access to the authentication ticket
- Cosign users to services they're authorized to access
-
-
Domain realm mapping (Kerberos but): Enter the domain DNS suffixes that should map to your realm. Use this setting when the DNS names of the hosts don't match the realm proper name. You most likely don't demand to create this custom domain-to-realm mapping.
-
PKINIT document (Kerberos only): Select the Public Key Cryptography for Initial Hallmark (PKINIT) certificate that can be used for Kerberos hallmark. You can cull from PKCS or SCEP certificates that you've added in Intune. For more information about certificates, see Use certificates for authentication in Microsoft Intune.
Wallpaper
You lot can experience unexpected behavior when a contour with no paradigm is assigned to devices with an existing image. For case, you create a contour without an epitome. This profile is assigned to devices that already have an epitome. In this scenario, the image may alter to the device default, or the original image may stay on the device. This behavior is controlled and limited past Apple's MDM platform.
Settings apply to: Automated device enrollment (supervised)
- Wallpaper Display Location: Choose a location on devices to evidence the image. Your options:
- Non configured: Intune doesn't change or update this setting. A custom image isn't added to devices. By default, the Os might set its own image.
- Lock screen: Adds the paradigm to the lock screen.
- Home screen: Adds the image to the abode screen.
- Lock screen and Dwelling screen: Uses the same image on the lock screen and home screen.
- Wallpaper Prototype: Upload an existing .png, .jpg, or .jpeg image you want to use. Be sure the file size is less than 750 KB. You lot can also remove an image that you lot added.
Tip
- When configuring a wallpaper policy, Microsoft recommends enabling the Block modification of Wallpaper setting. This setting prevents users from irresolute the wallpaper.
- To display different images on the lock screen and domicile screen, create a profile with the lock screen prototype. Create another profile with the home screen image. Assign both profiles to your iOS/iPadOS user or device groups.
Next steps
Assign the profile and monitor its status.
Y'all can also create device feature profiles for macOS devices.
Feedback
Submit and view feedback for
Source: https://docs.microsoft.com/en-us/mem/intune/configuration/ios-device-features-settings
0 Response to "Mdm Iphone Do Not Allow Images to Be Uploaded"
Post a Comment